Check and Validate Call Data Entries – 2816720764, 3167685288, 3175109096, 3214050404, 3348310681, 3383281589, 3462149844, 3501022686, 3509314076, 3522334406
This discussion centers on checking and validating the ten call data entries: 2816720764, 3167685288, 3175109096, 3214050404, 3348310681, 3383281589, 3462149844, 3501022686, 3509314076, and 3522334406. It emphasizes uniform schema, precise phone formats, and chronological timestamps, with attention to length, allowed characters, and plausible date ranges. Outcomes should be consistently encoded and auditable. The goal is repeatable workflows and anomaly detection that preserve data integrity as a foundation for subsequent quality improvements. The next steps will reveal where gaps emerge.
What This Dataset Tails: Understanding the 10 Call Entries
The dataset comprises ten call entries, each representing a discrete communication event with standardized fields and consistent formatting. The ten entries are cataloged by timestamp, caller, recipient, duration, and outcome, enabling cross-entry comparison.
Entries exhibit uniform schema, validation-ready values, and clear delimitation. This structure supports freedom in interpretation while preserving rigorous traceability and reproducible inspection across the dataset.
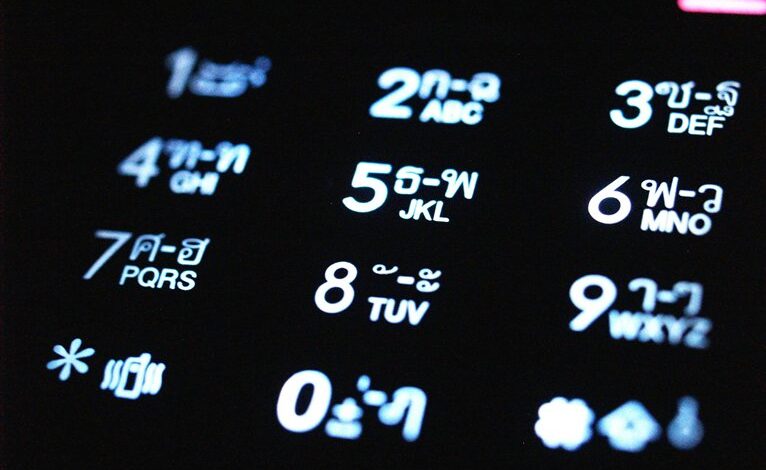
Core Validation Rules for Phone Numbers and Timestamps
Are phone numbers and timestamps subject to precise, uniform validation to ensure dataset integrity?
In this section, core validation rules establish consistent formats, length constraints, and character allowances for numbers, plus strict timestamp checks that confirm chronological order and plausible ranges.
The approach emphasizes reproducibility, error detectability, and auditable conformity, enabling reliable downstream analysis while preserving data freedom and interoperability across systems.
Practical Verification Steps and Quick Wins for Your Logs
Practical verification steps for log validation emphasize a concrete, repeatable workflow that quickly detects anomalies while preserving data integrity. This meticulous framework standardizes checks, documenting timestamps, cross-references, and field constraints. It acknowledges pragmatic shortcuts and quick wins, avoids invalid formatting pitfalls, and remains adaptable for freedom-oriented teams. Two word discussion ideas not relevant to the other H2s: concise rigor.
Ongoing Quality: Auditing, Anomaly Detection, and Maintenance
Ongoing quality encompasses systematic auditing, anomaly detection, and maintenance practices that sustain data integrity over time. The approach emphasizes repeatable procedures, traceable records, and defined thresholds to guide remedial actions. Audit anomalies are investigated with documented rationale, while continuous monitoring informs proactive adjustments. Maintenance dashboards consolidate metrics, ensuring transparency, accountability, and timely interventions across datasets and operational processes.
Conclusion
Beyond the numeric list lies a ledger of time and contact, each entry a pulse in a mechanical map. The validation process, like a careful loom, threads uniform formats through disparate data, aligning digits, dates, and encodings into one steady cadence. Anomalies drift to the surface as quiet ripples, ready for audit. With repeatable workflows and documented constraints, the dataset settles into a precise, auditable pattern—clear, predictable, and primed for ongoing quality surveillance.




